Post-Quantum Cryptography
How will we encrypt tomorrow?
Hanno Böck
https://hboeck.de
Introduction
Hanno Böck, freelance journalist and hacker.
Writing for Golem.de and others.
Fuzzing Project, funded by Linux Foundation's Core Infrastructure Initiative.
Author of monthly Bulletproof TLS Newsletter.
1982
Richard Feynman presents idea of a quantum computer
1994

Peter Shor shows quantum computers could break public key cryptography
Quantum computers
Well understood theory, but hard to engineer.
Some researchers give timeframes of 10-15 years for scalable quantum computers.
Post-Quantum Cryptography
Algorithms that we believe to be resistant to quantum attacks.
Development still in early stages.
Symmetric Post-Quantum Cryptography
Hash functions (SHA-2, SHA-3) and symmetric encryption (AES) are the easy part.
Just use larger keys (256 bit is fine).
Public key cryptography
- Encryption with separate public and private key
- Signatures
- Key exchanges
Underlying problems of public key cryptography
- Factoring-based (RSA)
- Discrete-logarithm-based (Diffie Hellman, DSA, ElGamal)
- Elliptic-curve-based (ECDSA, ECDH, X25519, Ed25519)
Quantum computers break all three.
Crypto is broken
Almost every crypto software and protocol today uses these algorithms.
TLS/SSL, SSH, OpenPGP/GnuPG, Signal, Whatsapp, OTR, OMEMO, ...
Quantum computers break practically everything using crypto.
Candidates for Post-Quantum Cryptography
Code-based cryptography
Lattice-based cryptography
Isogeny-based cryptography
Hash-based signatures
Multivariate cryptography
Conservative, safe choices
McEliece / McBits
McEliece: Code-based encryption.
Parameters from McBits paper (Bernstein, Chou, Schwabe, 2013).
Good: old, well researched
Bad: large keys (~1 MB)
Hash-based signatures
Good: as secure as the hash function
XMSS: needs internal state
SPHINCS: no state, but large signatures

Lattices
Ntru, Ring-Learning-With-Errors, New Hope, Ntru prime, BLISS, Tesla#.
Pro: Practical, fast, relatively small keys.
Con: Patents, conflicts over security estimates.
Most likely candidate for early deployments.
Supersingular Isogenies of Elliptic Curves
SIDH - Diffie-Hellman-alike key exchange.
Pro: Very similar workflow to Diffie Hellman, small keys.
Con: Not that fast, very new, needs more research.
Post-Quantum Cryptography today
We have the choice between very impractical and experimental algorithms.
Implementation considerationgs
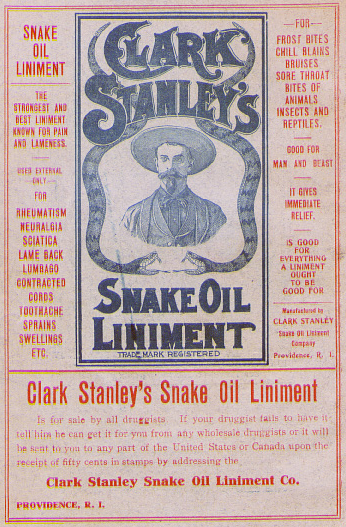
Attacks on old crypto



Logjam, FREAK, DROWN, SWEET32
Deprecation is hard
It often takes decades to deprecate old crypto. Windows-XP-compatibility is still a concern for some.
If quantum computers come in 10-15 years then the transition will be rough.
It's not just the algorithms
Secure algorithms can be used in insecure ways.
October 2016: Three research papers on potential backdoors and security issues with Diffie Hellman.
If we don't even know how to use the oldest public key algorithm safely, how should we know how to use entirely new algorithms?
Store now, decrypt later
Attackers could store large amounts of encrypted communication today and decrypt it once a quantum computer is available.
Strong argument for fast deployment.
Hybrid modes
No confidence in practical postquantum schemes.
Combine experimental postquantum algorithm with well researched prequantum algorithm.
Example: X25519 (elliptic curve) and New Hope (lattice-based) key exchange.
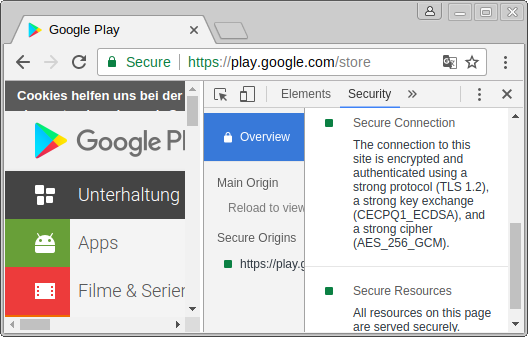
CECPQ1
Google deployed New Hope / X25519 hybrid in Chrome/BoringSSL and on some servers.
RebelAlliance
Hybrid New Hope / X25519 key exchange for tor.
Quantum Mythbusting
When will I have a quantum computer on my desk?
Maybe never.
Quantum algorithms
Quantum computers don't magically make everything faster, they're faster for very specific problems (factoring, physical simulations).
Even if possible: It's not clear if there's a need for home quantum computers.
Possible scenario: Quantum computers are run by universities and companies, one can rent computing time.
D-Wave
The D-Wave quantum computer can't run Shor's algorithm.
It's not clear if D-Wave quantum computers can do anything useful. But they are almost certainly irrelevant for cryptography.
Quantum Cryptography
Clarification of vocabulary
Quantum computing: Using quantum effects to solve mathematical problems that can't efficiently be solved on normal computers.
Post-Quantum cryptography: Cryptography that resists attacks with quantum computers.
Quantum cryptography / quantum key distribution: Using physical channels to exchange cryptographic keys.
Quantum cryptography / QKD
Idea: cryptography that is secure based on the laws of physics.
Send single particles with polarized encoding, exchange polarization filter configuration.
This has major drawbacks and solves nothing.
Huge hype
Latest trend: Talk about Quantum Internet.

Limitations
Very likely limited distances (tens or hundreds of kilometers).
Or maybe this is good?
Source: EU Quantum Manifesto
Trusted intermediates?

Quantum Internet?
Let's say I want to send an encrypted message from Berlin to Sydney.
Trusted intermediates in Poland, Ukraine, Russia, Kazakhstan, China, India, Burma, Thailand, Malaysia, Indonesia, Australia.
Not Wireless
QKD needs a physical connection between endpoints.
- No Wifi
- No mobile Internet
Quantum hacking
Quantum cryptography provides perfect security.
However regularly commercial QKD devices get broken.
How's that even possible?
QKD: Secure in theory
The big argument for QKD: It's perfectly secure - based on the laws of physics!
However that's only true for an idealized version of QKD, not for any real system.
Problems of hardware-based security
If you have a bug in your encryption software you can install an update (hopefully).
If you have a bug in your encryption hardware you need to buy new hardware.
QKD needs authentication
All QKD systems need an authenticated channel.
QKD depends on the cryptography its proponents claim it should replace.
This limitation is rarely mentioned, but it's significant. It means QKD can't solve the problems created by quantum computers.
Quantum cryptography
Extremely overhyped with outragerous claims ("Quantum Internet").
Entirely unclear which problems it should solve.
Definitely not a solution for the problems created by quantum computers. That solution is Post-Quantum cryptography.
Conclusions
Quantum computers may come pretty soon (or not at all). We need to be prepared.
Post-Quantum cryptography is still in its early stages. We're already too late.
Be wary of overhyped claims about quantum cryptography, which likely won't solve anything
More info
- pqcrypto.org
- pqcrypto.eu.org - EU PQCRYPTO research project
- csrc.nist.gov/groups/ST/post-quantum-crypto/ - NIST standardization effort
Questions?