TLS Version intolerance
Almost every imaginable TLS implementation flaw can be found in the wild.
Downgrades
SSL/TLS versions during handshake
Client: "Dear server, I support TLSv1.2"
Server: "I don't support that, let's use TLSv1.0"
But sometimes...
Client: "Dear server, I support TLSv1.2"
Server thinks: "I never heard of TLSv1.2... Maybe I better say nothing at all or send an error..."
Version intolerance (this is always a server bug)
Also...
Client tries to connect with highest version TLSv1.2 - Server wants SSLv3
Client tries to connect with highest version TLSv1.0 - Server will use TLSv1.0
What browsers did
Browser tries to connect with SSLv3 to TLSv1.2.
No answer? Browser retries with SSLv3 to TLsv1.1.
Retries all supported versions.
Behavior has been called "Protocol Dance".
Black Hat 2014
Antoine Delignat-Lavaud presents Virtual Host Confusion attack.
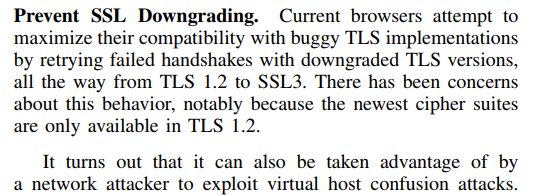
POODLE (2014)
Padding Oracle On Downgraded Legacy Encryption
Another Padding Oracle that only works against SSLv3.
Good for the attacker: We can downgrade users.
Solution
SCSV (RFC 7507): Server signals browser that it is not broken.
Protocol dance and SCSV
- We have a version negotiation mechanism
- Servers have broken TLS implementations.
- Browsers implement workaround.
- Workaround introduces security issue.
- Workaround for security issue introduced by workaround gets standardized.
Version intolerance
By now most browser downgrades have been removed.
"It's taken about 15 years to get to the point where web browsers don't have to work around broken version negotiation in TLS and that's mostly because we only have three active versions of TLS. When we try to add a fourth (TLS 1.3) in the next year, we'll have to add back the workaround, no doubt." Adam Langley (2016)
TLS 1.3 version intolerance
Around 3 % of servers affected.
Several vendors identified already, trying to pressure them to fix.